
Abstract
The increasing integration of software, artificial intelligence (AI), and connectivity in modern vehicles has expanded their attack surface, making cybersecurity a critical concern for the automotive industry. With vulnerabilities emerging in electronic control units (ECUs), remote access systems, vehicle-to-everything (V2X) communication, and over-the-air (OTA) software updates, regulatory bodies worldwide have introduced stringent cybersecurity frameworks. However, compliance remains complex due to fragmented regulations, supply chain security gaps, evolving cyber threats, and the financial burden of implementation.
This article provides a comparative analysis of key cybersecurity regulations, including UNECE WP.29, ISO/SAE 21434, NHTSA best practices, China’s GB/T 36628, and GDPR, outlining their enforcement levels, scope, and compliance challenges. Additionally, it discusses effective strategies such as secure-by-design development, AI-driven threat detection, blockchain-based authentication for supply chains, and standardized regulatory approaches. By adopting proactive security measures and fostering global collaboration, automakers can enhance compliance and mitigate cybersecurity risks in the evolving automotive landscape.
Introduction
The rapid evolution of connected and autonomous vehicles (CAVs) has transformed the automotive industry, offering enhanced convenience, safety, and efficiency. However, as vehicles become more software-dependent and interconnected, they also become high-value targets for cybercriminals. Modern vehicles house complex digital ecosystems, integrating cloud computing, wireless communication, and embedded systems, all of which introduce potential entry points for cyberattacks. These threats range from remote hijacking and data breaches to ransomware attacks on vehicle fleets, posing significant safety and privacy risks.
Recognizing these growing challenges, regulatory authorities across the globe have developed automotive cybersecurity standards to enforce security-by-design practices. However, automakers face hurdles in navigating multi-regional compliance requirements, securing supply chain integrity, and implementing cost-effective cybersecurity frameworks. This article delves into the global regulatory landscape, examining key cybersecurity standards, their challenges in enforcement, and the strategies that industry leaders must adopt to safeguard the next generation of connected vehicles.
Key Automotive Cybersecurity Regulations
- UNECE WP.29 – R155 and R156
The United Nations Economic Commission for Europe (UNECE) WP.29 established Regulation No. 155 (R155) and Regulation No. 156 (R156) to mandate cybersecurity and software update requirements for vehicles.
The United Nations Economic Commission for Europe (UNECE) WP.29 established Regulation No. 155 (R155) and Regulation No. 156 (R156) to mandate cybersecurity and software update requirements for vehicles. These regulations apply to all UNECE member states, including the European Union, Japan, South Korea, and others, impacting global automakers.
R155 requires automakers to establish and maintain a robust cybersecurity management system (CSMS) that covers the entire vehicle lifecycle. This includes conducting threat analysis and risk assessments (TARA) to identify vulnerabilities and mitigate risks. Automakers must enforce real-time monitoring and incident response mechanisms to detect and address cyber threats proactively. Furthermore, periodic third-party audits are mandated to verify cybersecurity compliance before type approval.
R156 ensures that over-the-air (OTA) and manual software updates follow stringent security protocols. Vehicle manufacturers must maintain log records of all software updates, ensuring traceability and security. The regulation also addresses risks associated with rollback attacks, preventing unauthorized or outdated software versions from being reinstated. Robust authentication and encryption methods are required to safeguard updates from cyber threats.
These regulations became mandatory for all new vehicle models in July 2022. By July 2024, all newly manufactured vehicles must comply with these regulations, or they will not receive regulatory approval in UNECE member states.
- ISO/SAE 21434: Road Vehicles – Cybersecurity Engineering
This international standard, developed jointly by the International Organization for Standardization (ISO) and the Society of Automotive Engineers (SAE), establishes best practices for automotive cybersecurity engineering. It covers cybersecurity across the entire vehicle development lifecycle, from concept and design to decommissioning.
ISO/SAE 21434 encourages automakers to conduct systematic risk assessments and penetration testing to identify vulnerabilities early in the development phase. It uses a TARA (Threat Analysis and Risk Assessment) framework to analyze potential cybersecurity threats in automotive systems. The standard aligns with UNECE WP.29 R155, making it a key reference for meeting regulatory compliance. It also introduces the concept of cybersecurity governance, requiring manufacturers to define roles and responsibilities for cybersecurity management. Additionally, the standard stresses the importance of secure coding practices, encryption, and authentication protocols to safeguard automotive networks.
- NHTSA Cybersecurity Best Practices
The National Highway Traffic Safety Administration (NHTSA) in the United States has released non-binding cybersecurity guidelines for automakers and suppliers. Although not enforceable as law, they serve as a foundation for cybersecurity strategies in the automotive industry.
NHTSA recommends a defense-in-depth strategy, which layers multiple cybersecurity controls to protect vehicle systems. The guidelines emphasize the importance of cryptographic protections for in-vehicle communications and software updates. Automakers are encouraged to implement secure boot mechanisms to prevent unauthorized code execution and secure data logging and event recording to facilitate cybersecurity incident investigations.
Additionally, NHTSA suggests establishing an industry-wide vulnerability disclosure program, allowing cybersecurity researchers and stakeholders to report security flaws effectively. The guidelines also urge the automotive industry to adopt real-time intrusion detection systems to identify and mitigate cybersecurity threats before they impact vehicle functionality.
- China’s GB/T 36628 and MIIT Guidelines
China has developed its own set of cybersecurity standards for intelligent and connected vehicles under GB/T 36628 and regulations enforced by the Ministry of Industry and Information Technology (MIIT).
These regulations require strong identity authentication mechanisms, ensuring that only authorized devices can access vehicle systems. They enforce data encryption standards to protect sensitive vehicle and driver information from unauthorized access. Security protocols for vehicle-to-cloud (V2C) and vehicle-to-everything (V2X) communications are mandated to minimize the risk of remote cyberattacks.
China’s regulations also impose stringent data storage and transmission policies, limiting exposure to data breaches. Automakers must adhere to cybersecurity testing and certification processes before vehicles are approved for mass production. MIIT further promotes the establishment of national cybersecurity testing centers to evaluate vehicle security before public deployment, ensuring that cybersecurity threats are mitigated before commercialization.
- European General Data Protection Regulation (GDPR) and Automotive Cybersecurity
While not a cybersecurity regulation specifically for vehicles, GDPR plays a crucial role in automotive cybersecurity due to the extensive collection of driver and vehicle data.
GDPR requires automakers and technology providers to implement privacy-by-design principles to protect user data. It mandates clear data processing transparency, ensuring users are informed about how their data is collected, stored, and used. The regulation also introduces strict data breach notification rules, requiring organizations to report breaches within 72 hours of detection.
Failure to comply with GDPR can result in severe penalties, with fines reaching up to 4% of global annual revenue. This regulation ensures that automakers take data security seriously, reducing the risk of data-driven cyberattacks that could compromise user privacy.
While multiple cybersecurity regulations exist worldwide, their implementation and scope vary across regions. Below is a comparative overview:
|
Region |
Enforcement |
Key Focus Areas |
Compliance Deadline |
|
|
UNECE WP.29 |
Europe, Japan, Korea |
Mandatory |
CSMS & SUMS |
July 2022 / 2024 |
|
|
ISO/SAE 21434 |
Global |
Industry Standard |
Risk Assessment, Secure Design |
No enforcement |
|
|
NHTSA |
USA |
Non-binding |
Best Practices |
N/A |
|
|
China’s GB/T 36628 |
China |
Mandatory |
Data security, encryption |
Ongoing |
|
|
GDPR |
Europe |
Mandatory |
|
Varies by Country |
The following graph visually compares these regulations based on their enforcement level, key focus areas, and compliance urgency. This highlights how different regions prioritize various aspects of cybersecurity compliance.
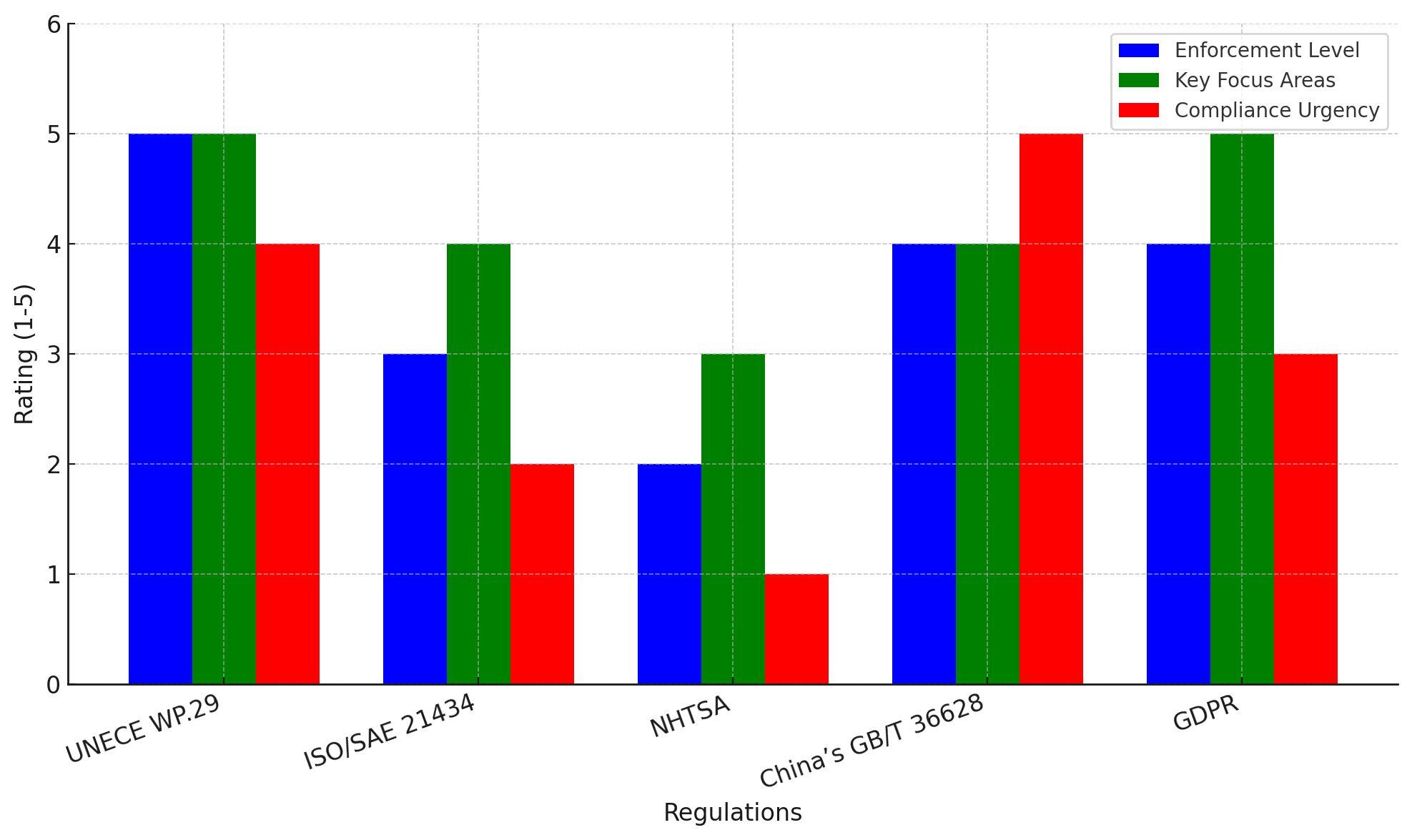
Figure 1: Comparative Analysis of Automotive Cybersecurity Regulations
Challenges in Compliance
- Complexity of the Automotive Supply Chain
The automotive industry operates through an intricate and multi-tiered supply chain, making cybersecurity compliance particularly challenging. Modern vehicles incorporate components from various suppliers, each of whom may have different cybersecurity policies and practices. Ensuring a standardized security framework across OEMs, Tier 1, and Tier 2 suppliers is a monumental task. Research published in IEEE Transactions on Intelligent Transportation Systems highlights that the lack of uniform cybersecurity implementation within supply chains can create vulnerabilities that attackers can exploit at the weakest link. Moreover, with global sourcing of parts, varying regulatory requirements across regions add another layer of complexity, requiring manufacturers to continuously audit and monitor their suppliers to maintain compliance.
- Evolving Cyber Threats
Cyber threats in the automotive sector are evolving at an unprecedented rate, requiring constant vigilance and updates to security protocols. Unlike traditional vehicles, modern software-defined vehicles (SDVs) rely on complex electronic control units (ECUs) and cloud-based services, increasing their attack surface. Studies from Springer’s Journal of Cybersecurity suggest that real-time monitoring and threat intelligence sharing are crucial for identifying emerging threats, yet many manufacturers struggle to implement proactive measures. Attack vectors such as CAN bus intrusions, remote keyless entry exploits, and vehicle-to-everything (V2X) communication vulnerabilities necessitate continuous updates. However, keeping up with such threats while maintaining regulatory compliance demands significant resources, which not all companies can afford.
- High Costs of Compliance
Ensuring full compliance with automotive cybersecurity regulations is an expensive undertaking. Research from MDPI’s Sensors Journal indicates that cybersecurity costs in the automotive industry include hardware security modules (HSMs), secure over-the-air (OTA) update mechanisms, penetration testing, and workforce training. Many smaller suppliers struggle to allocate the necessary resources for compliance, leading to disparities in security implementation across the supply chain. Furthermore, ongoing costs associated with continuous monitoring, cybersecurity audits, and vulnerability patching add to the financial burden. While major automakers can afford dedicated cybersecurity teams, smaller Tier 2 and Tier 3 suppliers may lack the necessary expertise, making compliance difficult to sustain.
- Regulatory Fragmentation Across Regions
Global automakers must comply with an array of cybersecurity regulations, from UNECE WP.29 in Europe to ISO/SAE 21434, China’s GB/T 36628, and NHTSA’s best practices in the U.S. Each of these frameworks has unique requirements, and ensuring compliance across different regulatory jurisdictions can be highly demanding. According to a study published in ScienceDirect’s Transportation Research, the lack of harmonization between global cybersecurity regulations leads to inefficiencies in compliance, causing delays in vehicle deployment. For instance, an automaker complying with WP.29 may still need to implement separate cybersecurity measures for the U.S. market, requiring additional testing and documentation, which increases costs and development time.
- Over-the-Air (OTA) Update Security
Over-the-air (OTA) software updates are essential for maintaining vehicle security and ensuring compliance with evolving regulations. However, they also present significant cybersecurity risks. Unauthorized access to an OTA update system could allow attackers to deploy malicious firmware, compromising vehicle functionality and safety. According to research published in IEEE Xplore, ensuring secure OTA updates requires robust encryption, authentication, and rollback protection mechanisms. Despite these safeguards, implementing secure OTA frameworks across different vehicle models and ECU architecture is a complex process. Manufacturers must ensure that OTA systems comply with ISO/SAE 21434 and UNECE WP.29 requirements, which mandate secure update management and auditing procedures. However, real-world incidents of OTA update failures, such as software bugs leading to vehicle recalls, demonstrate the challenges of balancing security, reliability, and regulatory compliance.
As vehicles become increasingly connected and software-driven, their attack surfaces have expanded significantly. Hackers can exploit multiple entry points, including ECUs (Electronic Control Units), remote key access, infotainment systems, and V2X communication modules. These vulnerabilities pose serious risks, from data breaches to unauthorized vehicle control. The following diagram illustrates the key potential attack surfaces in modern vehicles, highlighting the complexity of securing automotive cybersecurity systems.
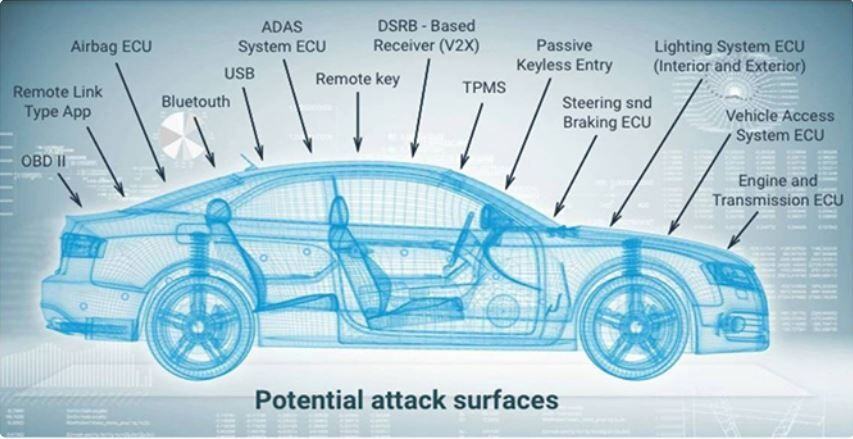
Figure 2: Potential attack surfaces in a connected car. Source: KPIT
Strategies for Strengthening Compliance
- Adopting a Secure-by-Design Approach
Integrating cybersecurity measures from the initial stages of vehicle design ensures that security is foundational rather than an afterthought. This proactive approach involves conducting comprehensive Threat Analysis and Risk Assessments (TARA) during development to identify potential vulnerabilities early.
Automakers such as Tesla and Toyota have adopted secure-by-design principles by integrating secure boot mechanisms, cryptographic key management, and real-time anomaly detection into their vehicle software architectures. Implementing these security measures at the software development stage reduces the risk of cyber threats in production vehicles and aligns with compliance requirements from ISO/SAE 21434 and UNECE WP.29. Furthermore, manufacturers should implement penetration testing methodologies, like those recommended by NIST Cybersecurity Framework, to simulate real-world attack scenarios and harden vehicle defenses.
- Enhancing OTA Security Measures
Over-the-Air (OTA) updates are critical for modern vehicles but securing them is a challenge. To ensure OTA updates remain secure, manufacturers must implement:
- Digital signature verification using cryptographic algorithms like RSA/ECC to validate update authenticity.
- Firmware rollback prevention mechanisms to block outdated or compromised software versions from being reinstalled.
- End-to-end encryption for OTA transmission to prevent data interception.
A notable example is Tesla’s OTA update security model, which employs cryptographic authentication and segmented update deployment to mitigate cybersecurity risks.
- Implementing Continuous Monitoring
Establishing robust systems for continuous monitoring allows for early detection of anomalies and potential cyber threats. Automotive Intrusion Detection and Prevention Systems (IDPS) should be integrated within vehicle networks to detect malicious activities in real time. AI-driven monitoring tools, such as those utilized by General Motors and Volkswagen, use machine learning models to analyze behavioral patterns and detect deviations from expected operations.
Incident response plans must be clearly defined and regularly tested to ensure rapid mitigation of cyber threats. Automakers should leverage industry best practices, such as MITRE ATT&CK for Automotive, to develop threat intelligence strategies. Additionally, collaboration with governmental cybersecurity agencies and private-sector threat intelligence firms can improve response capabilities and compliance alignment.
- Foster Collaboration Across the Supply Chain
Given the complexity of automotive supply chains, fostering collaboration among all stakeholders is crucial. Manufacturers must work closely with suppliers to ensure uniform cybersecurity implementation across Tier 1, Tier 2, and Tier 3 suppliers. Shared cybersecurity standards such as ISO/SAE 21434 should be mandated in supplier contracts to guarantee adherence to secure development practices.
Companies such as Ford and BMW have introduced supplier cybersecurity auditing programs, where suppliers must undergo cybersecurity maturity assessments before being approved for production partnerships. Additionally, implementing blockchain-based authentication mechanisms for parts traceability can enhance security in the supply chain by preventing counterfeit or tampered components from entering vehicle production.
- Invest in Workforce Training and Development
A well-trained workforce is essential for maintaining cybersecurity compliance. Investing in ongoing cybersecurity training programs ensures that employees are equipped to handle emerging threats. Automakers should establish dedicated cybersecurity centers of excellence (CCoE) to foster continuous learning, hands-on training, and security certification programs for engineers and IT personnel.
Case studies from Daimler and Honda reveal that integrating red-team exercises stimulated cyberattacks on vehicle software has improved incident detection and response times. Partnering with universities and research institutions to offer automotive cybersecurity training will also help bridge the current talent gap in this rapidly evolving field.
- Engage in Active Participation with Regulatory Bodies
Maintaining open lines of communication with regulatory bodies allows manufacturers to stay abreast of evolving standards and expectations. Active participation in industry forums and working groups provides insights into upcoming regulatory changes and offers opportunities to influence policy development. This proactive engagement ensures that manufacturers can anticipate and prepare for new compliance requirements, thereby avoiding potential pitfalls.
By implementing these strategies, automotive manufacturers can enhance their cybersecurity posture, ensuring compliance with regulations and safeguarding against emerging threats.
Conclusion
As vehicles become more connected and software-driven, cybersecurity regulations will continue to evolve. Compliance with frameworks such as UNECE WP.29, ISO/SAE 21434, NHTSA best practices, and GDPR is crucial for securing modern vehicles against cyber threats. However, automakers face significant challenges, including supply chain security gaps, the rapid evolution of cyber threats, high compliance costs, and regional regulatory fragmentation.
To navigate these complexities, automakers, policymakers, and cybersecurity experts must take proactive measures to strengthen compliance and security strategies. Here are three key focus areas for the next five years:
- Automakers must invest in AI-driven cybersecurity solutions – As threats become more sophisticated, real-time intrusion detection and machine learning-based anomaly detection will be essential for predictive cybersecurity in connected vehicles.
- Regulators need to work toward harmonizing global cybersecurity standards – Differences between UNECE WP.29, NHTSA, and China’s GB/T 36628 create compliance bottlenecks. Aligning regulatory frameworks will reduce complexity for global automakers and accelerate secure innovation.
- Supply chains must integrate blockchain-based authentication – Ensuring traceability of vehicle components using blockchain can prevent counterfeit ECUs, mitigate third-party cybersecurity risks, and establish end-to-end supply chain transparency.
The future of automotive cybersecurity lies in continuous adaptation, industry-wide collaboration, and technology-driven solutions. By adopting secure-by-design principles, leveraging AI-powered cybersecurity tools, and participating in global regulatory discussions, automakers can build safer, cyber-resilient vehicles while ensuring compliance with evolving cybersecurity mandates.







